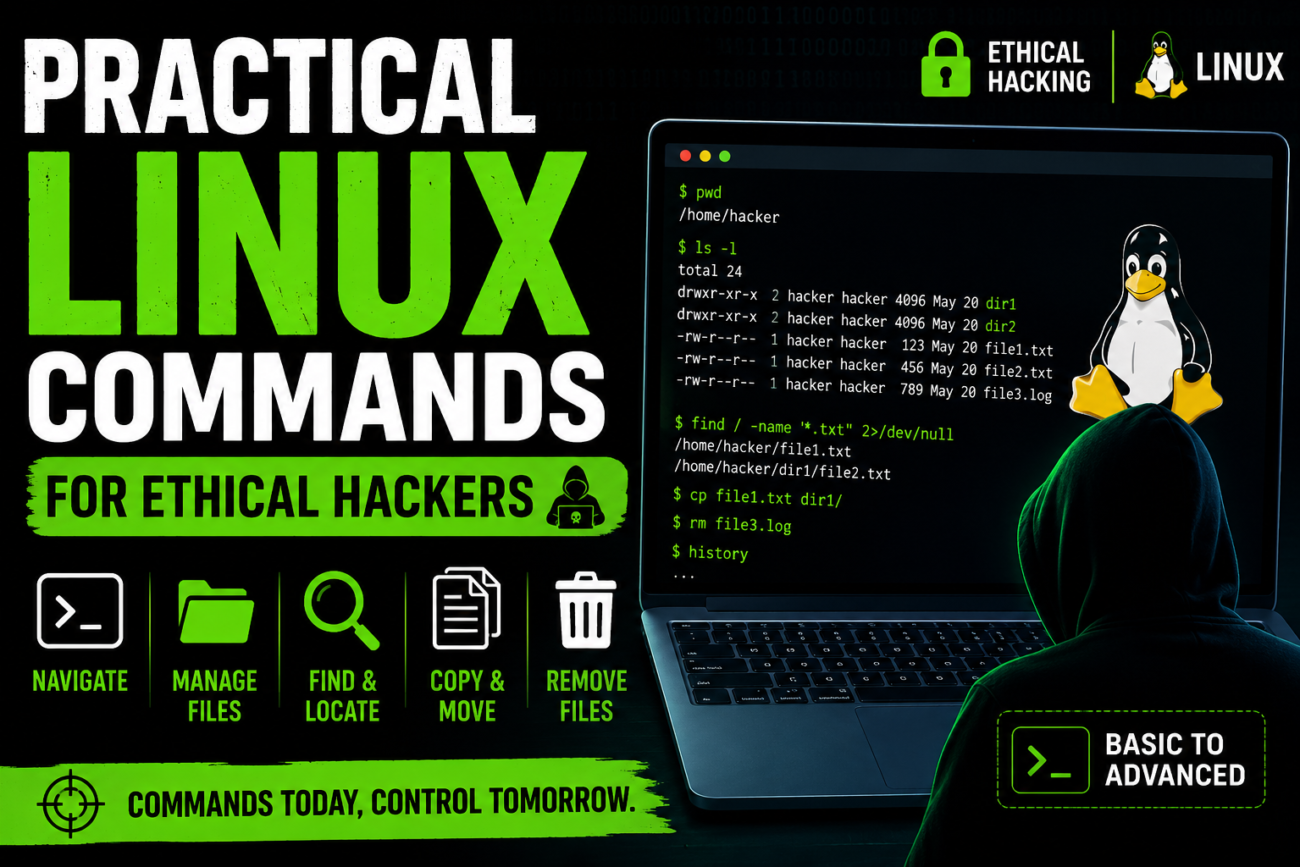
Question -1 Part 1: File System Structure & Navigation • Explore root directory using:pwdls /ls -l … Practical Linux Commands for Ethical HackersRead more
Working with Lists in Python – Chapter 4
Python Crash Course Series Python में Lists सीखने के बाद अगला सबसे important concept आता है … Working with Lists in Python – Chapter 4Read more
Python If Statements Explained in Hindi | Beginner Friendly Tutorial | Cyber-Teck
Python में If Statement क्या होता है? Programming में कई बार हमें किसी condition (शर्त) को … Python If Statements Explained in Hindi | Beginner Friendly Tutorial | Cyber-TeckRead more
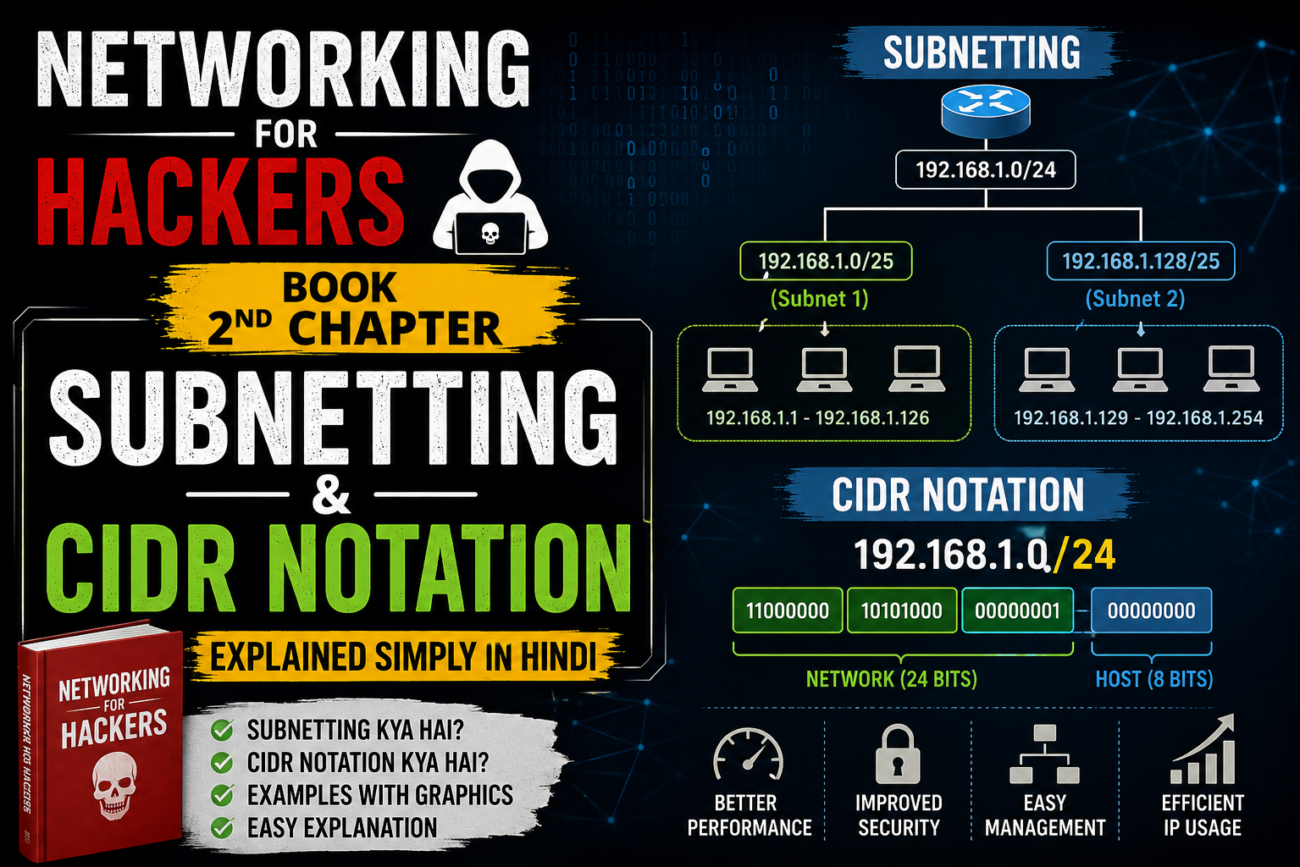
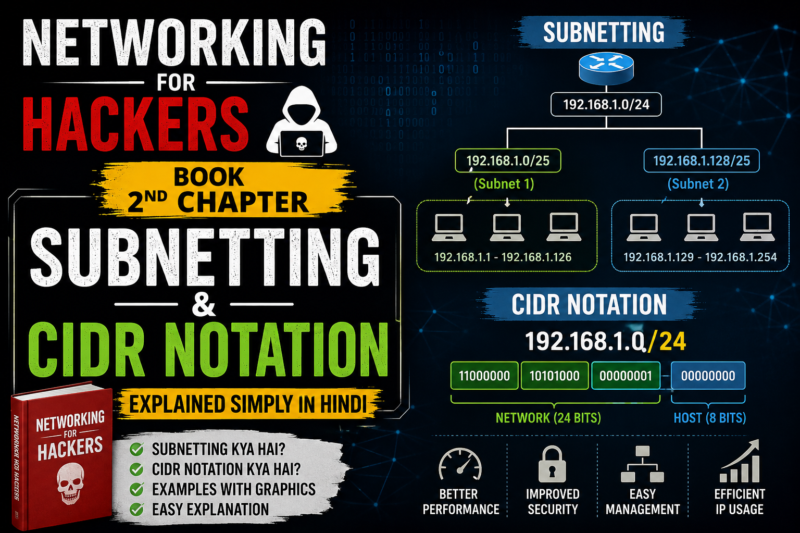
Subnetting and CIDR Notation | Networking for Hackers Book 2nd Chapter
Subnetting Kya Hota Hai? Subnetting ka matlab hota hai:👉 Ek bade network ko chhote-chhote networks me … Subnetting and CIDR Notation | Networking for Hackers Book 2nd ChapterRead more
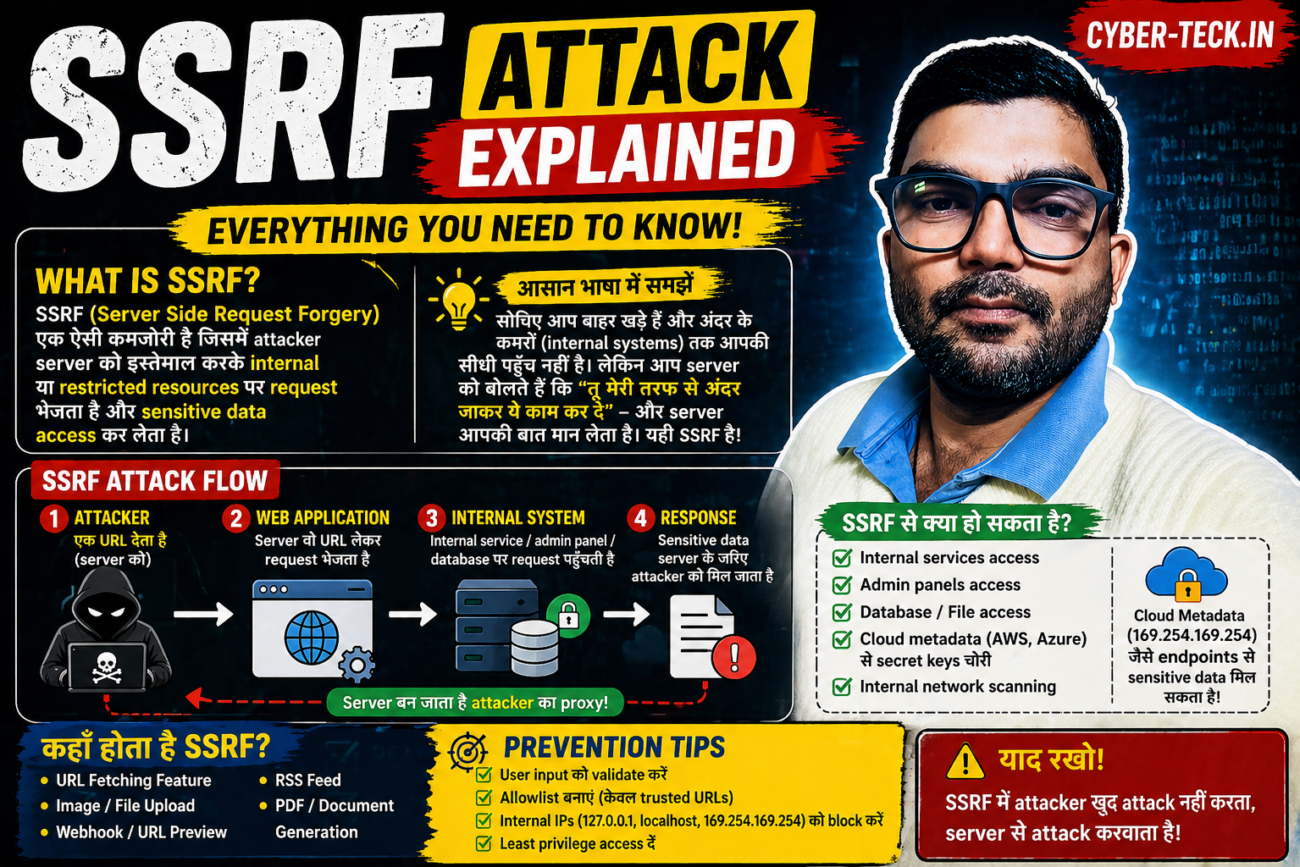
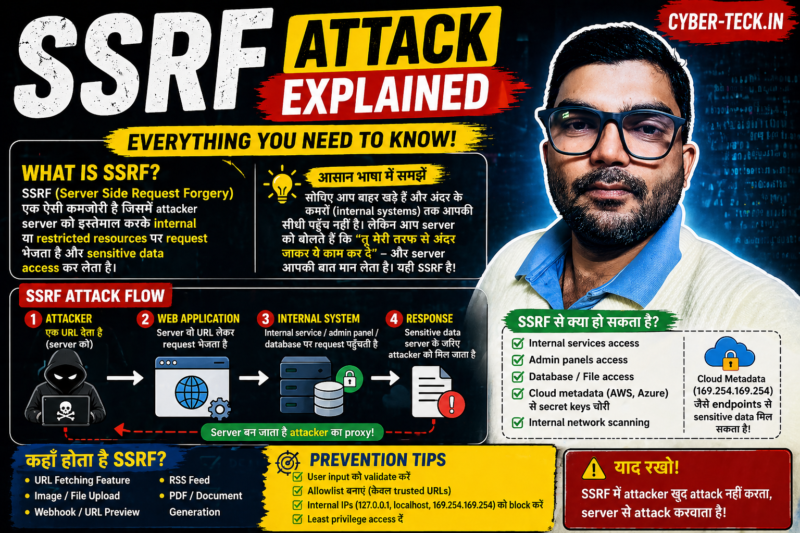
SSRF (Server Side Request Forgery) – Picture ke sath easy explanation
SSRF क्या है? 👉 SSRF = Server Side Request Forgery 👉 मतलब: Attacker server को बोलता … SSRF (Server Side Request Forgery) – Picture ke sath easy explanationRead more
Windows में FoxyProxy + Burp Suite CA Certificate Setup (Step-by-Step Guide with Images)
Introduction Agar aap ethical hacking / bug bounty / web security testing seekh rahe ho, to … Windows में FoxyProxy + Burp Suite CA Certificate Setup (Step-by-Step Guide with Images)Read more
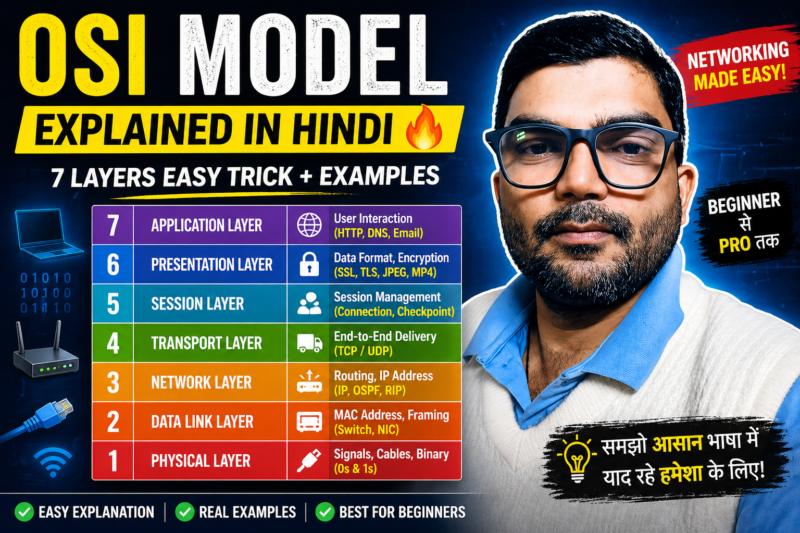
OSI Model Explained in Hindi (Beginner to Pro Guide)
🔰 Introduction OSI Model (Open Systems Interconnection Model) networking ka ek standard framework hai jo batata … OSI Model Explained in Hindi (Beginner to Pro Guide)Read more
Burp Suite Installation (Mac M1/M2/M3/M4 + Kali Linux) & FoxyProxy Setup Guide
Introduction Agar aap Cyber Security ya Ethical Hacking start kar rahe ho, to Burp Suite Community … Burp Suite Installation (Mac M1/M2/M3/M4 + Kali Linux) & FoxyProxy Setup GuideRead more
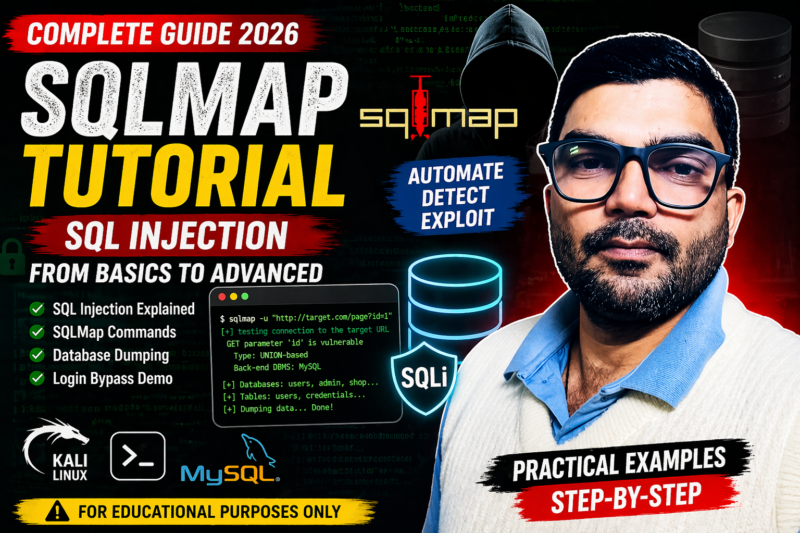
SQLMap Basics – SQL Injection Attack Ka Complete Guide (Beginner to Advanced)
Introduction Cyber Security में SQL Injection एक बहुत ही dangerous vulnerability है। Hackers इसी technique का … SQLMap Basics – SQL Injection Attack Ka Complete Guide (Beginner to Advanced)Read more
Network Basics for Hackers (Beginner Guide)
Cyber Security शुरू करने से पहले ये ज़रूरी क्यों है? अगर आप Ethical Hacking या Cyber … Network Basics for Hackers (Beginner Guide)Read more